Deep Intelligent AI Analysis
Deep Intelligent AI: A Comprehensive Security Analysis Tool
Application Overview
The Acquisition Framework is a powerful, modular web-based security analysis tool designed to provide a comprehensive suite of reconnaissance, footprinting, and vulnerability assessment capabilities. Developed using a robust Python and Flask backend, it features a dynamic and user-friendly single-page application interface that allows for the real-time execution and monitoring of a wide range of security scans. Its primary purpose is to consolidate the power of numerous industry-standard hacking and security tools into a single, accessible platform, enabling a systematic and in-depth investigation of a target domain’s security posture. The framework is designed to run locally, ensuring all data and operations remain secure and private on the user’s machine.
Core Purpose and Objectives
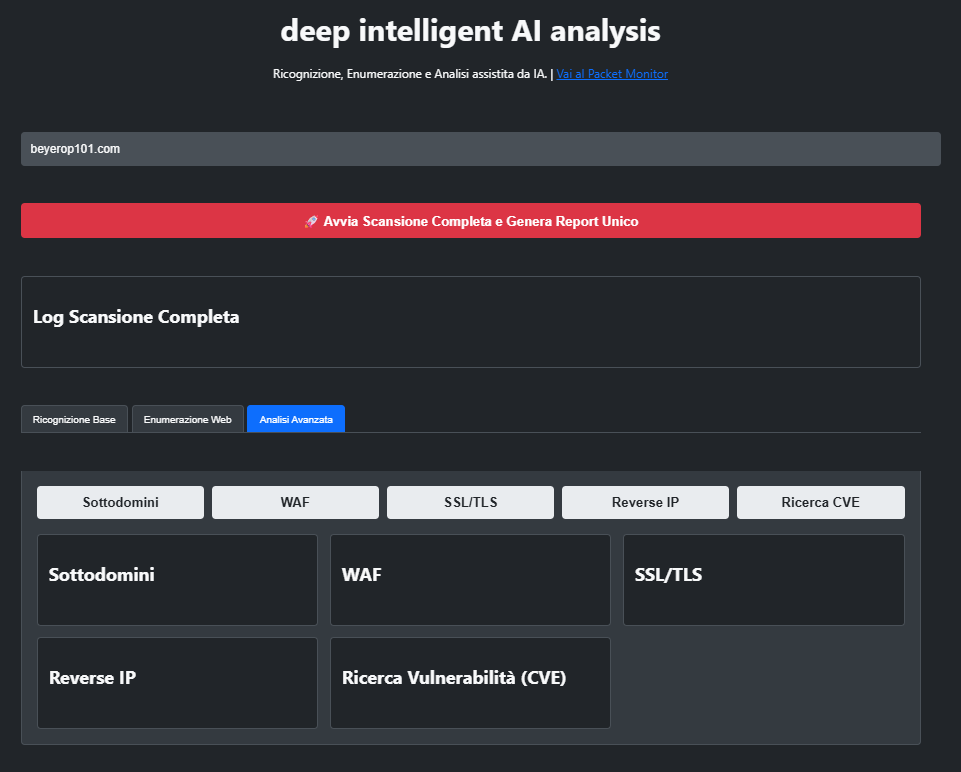
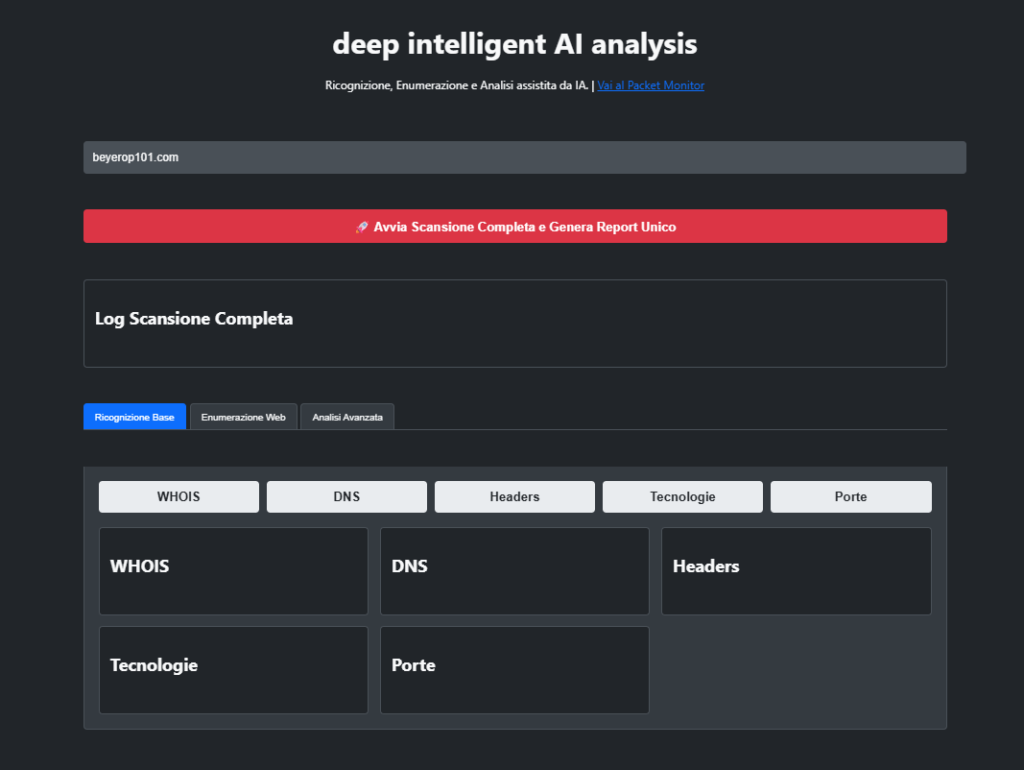
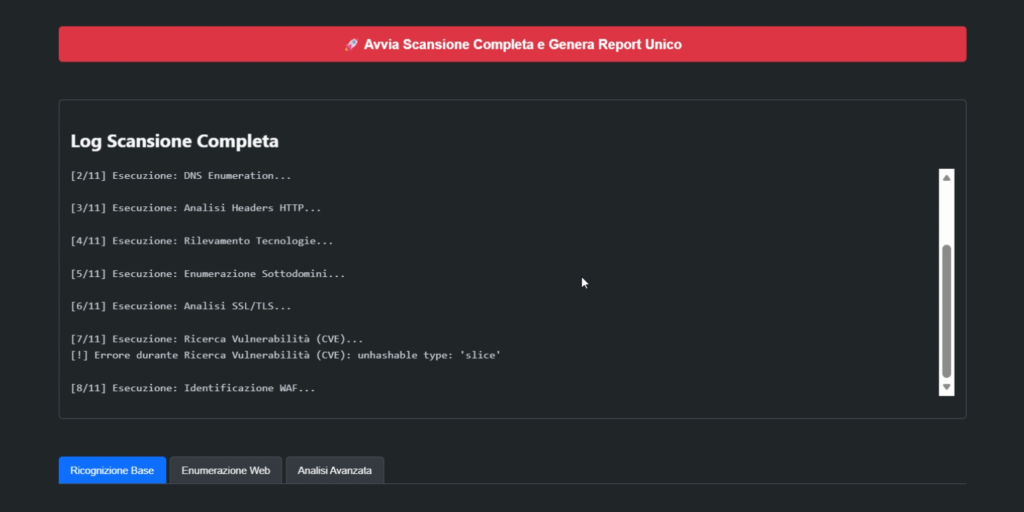
The primary objective of the Acquisition Framework is to automate and streamline the critical initial phases of a security audit or penetration test. It aims to provide a clear and detailed picture of a target’s attack surface by gathering information from disparate sources and actively probing for weaknesses. Its objectives are threefold:
- Discover and Map: Create a comprehensive and accurate map of the target’s digital infrastructure, including its domains, subdomains, IP addresses, running services, and the technologies it relies upon.
- Identify Vulnerabilities: Actively test the identified infrastructure for known vulnerabilities, misconfigurations, and weaknesses, ranging from outdated server software to critical injection flaws like SQL Injection.
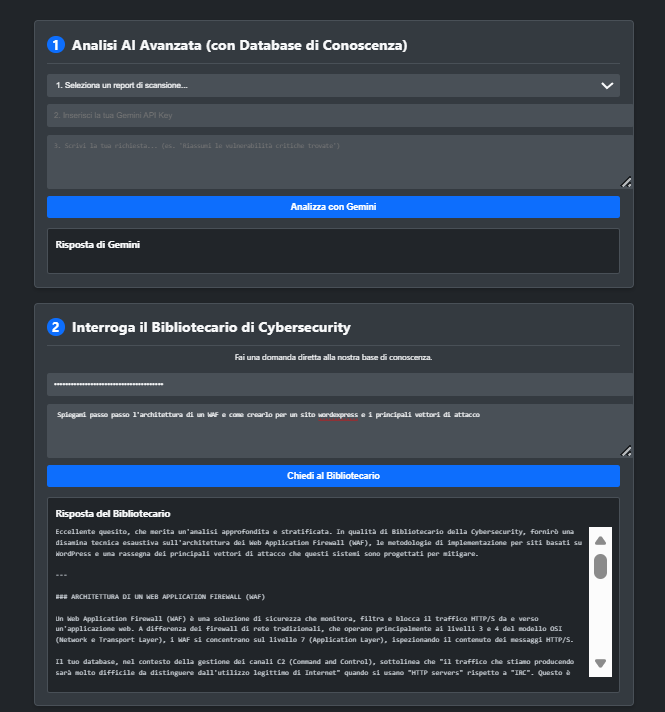
- Consolidate Intelligence: Gather all collected data into a single, comprehensive report that can be easily analyzed, whether by a human operator or integrated artificial intelligence modules, to derive actionable security insights.
Deep Intelligent AI Analysis
Target Audience and Intended Use
This tool is designed for a specific set of users who require a deep technical understanding of a web application’s security:
- Penetration Testers and Ethical Hackers: As a primary tool for the reconnaissance and information gathering phase, it automates many of the repetitive tasks involved in mapping an attack surface, allowing testers to focus on exploitation and analysis.
- Security Students and Researchers: As an educational platform, it provides a hands-on environment to learn and understand how different security tools work and how their data can be correlated. It serves as an excellent practical component for academic theses and cybersecurity projects.
- System Administrators and Developers: For defensive purposes, it allows them to perform a ‘self-assessment’ of their own websites and applications, helping them to see their infrastructure from an attacker’s perspective and identify potential security flaws before malicious actors do.
How the Framework Enhances Security
The Acquisition Framework directly contributes to security improvement by providing a structured and proactive approach to vulnerability discovery:
- From an Offensive Perspective (Red Team): The tool significantly improves the efficiency of an attack simulation. By automating the discovery of subdomains, open ports, running services with specific versions, and potential injection points, it provides the attacker with a rich list of potential targets. For example, by identifying a specific web server version (e.g., Apache 2.4.41), the framework allows the user to immediately search for known exploits for that version. By discovering a module on a forgotten subdomain, it provides SQLMap with a new target to test for database vulnerabilities. This methodical approach increases the likelihood of finding a valid entry point into the system.
- From a Defensive Perspective (Blue Team): The true value of the framework lies in its ability to be used for defensive security audits. A system administrator can run the entire suite of scans against their own domain to answer critical questions:
- Do I have forgotten subdomains (dev.mysite.com) running old, unpatched code? The subdomain enumeration module will find them.
- Is my server exposing sensitive ports to the internet? The advanced Nmap scan will reveal them.
- Is my HTTPS configuration strong, or am I using weak and outdated protocols? The SSL/TLS analysis will provide a clear grade and a detailed report.
- Are my contact forms vulnerable to SQL Injection or basic XSS attacks? The web vulnerability scanners and SQLMap will test them.
By proactively identifying these weaknesses, the framework enables developers and administrators to patch vulnerabilities, strengthen configurations, and reduce the overall attack surface before a real attacker has the chance to exploit them. It transforms security from a reactive process (fixing problems after a breach) into a proactive one (finding and resolving weaknesses before they can be exploited). The integration of AI for report analysis further accelerates this process, allowing users to quickly extract the most critical findings from a large volume of scan data.
